What is HeartBleed Bug? And Why You Should Care

Heartbleed is a major vulnerability in open-source software OpenSSL, a technology used to provide encryption of an estimated 66% of all servers on the public Internet. OpenSSL is an open source code that is developed and maintained by a community of developers, rather than by a single company.
Heartbleed can reveal the contents of a server’s memory, where the most sensitive of data is stored. That includes private data such as usernames, passwords, and credit card numbers. Thus through this bug, hackers / bot can access to user’s passwords and fool people into using bogus version of Web sites.
The bug was reportedly discovered on Monday (7 April 2014) by a member of Google’s security team and a software security firm called Codenomicon.
The bug affects web servers running Apache and Nginx software, and it has the potential to expose private information users enter into websites, applications, web email and even instant messages.
How this is Major?
Security vulnerabilities come and go, but this one is extremely serious. Not only does it require significant change at Web sites, it could require anybody who’s used them to change passwords too, because they could have been intercepted. That’s a big problem as more and more of people’s lives move online, with passwords recycled from one site to the next and people not always going through the hassles of changing them.
While most security experts advise that you always use websites and services offering SSL security encryption whenever possible, the Heartbleed bug has the ability to allow malicious operators to defeat this security layer and capture passwords as well as forge authentication cookies and obtain other private information.
When the bug is exploited the attacker can retrieve memory (up to 64kb) from the remote system. This memory may contain usernames, passwords, keys or other useful information that enables bigger attacks. An attacker may for example be able to retrieve the keys and secrets used to encrypt traffic and then intercept and read the communications of all other users of that service. There are all kinds of variations that might be possible based on the ability to read this memory. 64kb may not seem like a great deal of data, but of course the attacker can connect repeatedly and progressively collect more information. This is a serious problem indeed. (credit)
How to check a site’s Heartbleed vulnerability?
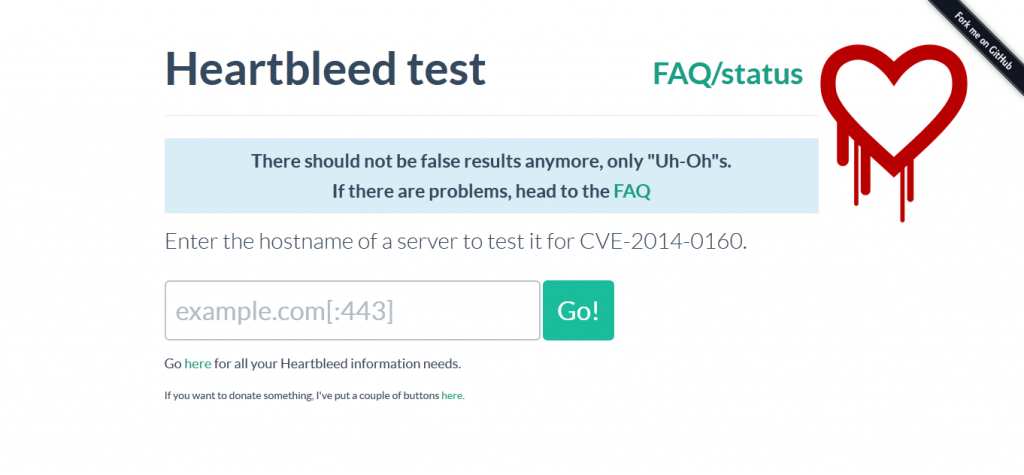 Developer and cryptography consultant Filippo Valsorda published a tool that lets people check Web sites for Heartbleed vulnerability. That tool showed Google, Microsoft, Twitter, Facebook, Dropbox, and several other major Web sites to be unaffected — but not Yahoo. Valsorda’s test uses Heartbleed to detect the words “yellow submarine” in a Web server’s memory after an interaction using those words.
Developer and cryptography consultant Filippo Valsorda published a tool that lets people check Web sites for Heartbleed vulnerability. That tool showed Google, Microsoft, Twitter, Facebook, Dropbox, and several other major Web sites to be unaffected — but not Yahoo. Valsorda’s test uses Heartbleed to detect the words “yellow submarine” in a Web server’s memory after an interaction using those words.
If you have a site with SSL then you should probably care, because your site and its clients are under threat about sensitive information and data such as login credentials and credit card information.
3 things to do against Heartbleed protection
- Wait for an official announcement from any secure website or service that you normally use regarding a security update.
- After you’ve confirmed that the site or service has installed a security update, change your passwords.
- For at least the next week, keep an eye on any of your sensitive online accounts (banking, webmail) for suspicious activity. (tips from mashable)
Security Patch
A security patch for the bug was announced by OpenSSL.
Keeping an eye on the breaking news on Heartbleed
Follow Google news on the topic of Heartbleed to be in the know and latest developments.
Read more:
* Diagnosis of the OpenSSL Heartbleed Bug
Check out our Pinterest Board on HeartBleed:
//assets.pinterest.com/js/pinit.js